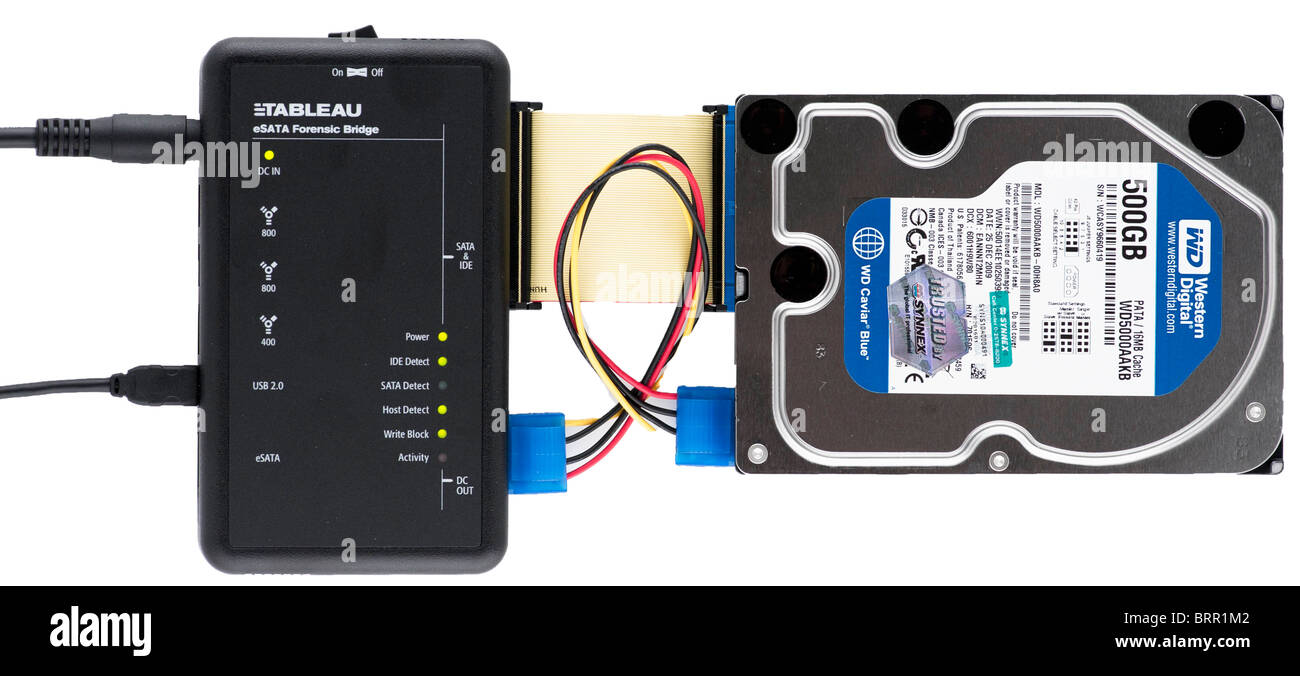
1 Using forensic write-blocking hardware to acquire a disk image of a... | Download Scientific Diagram
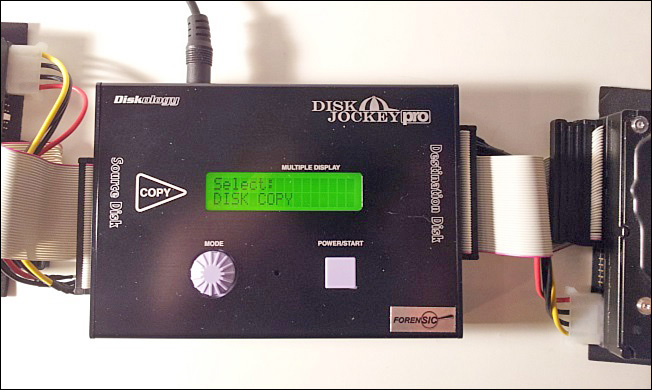
Cloning a PATA or SATA Hard Disk | Handling Computer Hardware in a Computer Forensics Investigation | Pearson IT Certification

Cloning a PATA or SATA Hard Disk | Handling Computer Hardware in a Computer Forensics Investigation | Pearson IT Certification
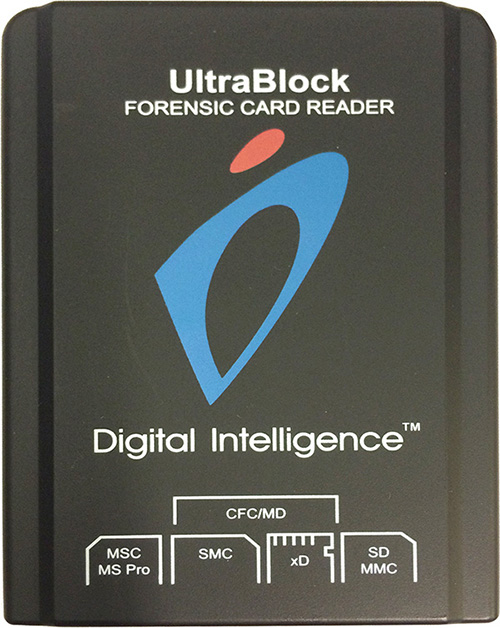
Removable Memory | Handling Computer Hardware in a Computer Forensics Investigation | Pearson IT Certification